I — The Mandate
In 1994, Congress passed the Communications Assistance for Law Enforcement Act — CALEA. Its requirement was precise: telecommunications companies must redesign their networks to enable government wiretapping by design. Not as an option. Not on request. As a structural feature, built in before the product ships.
That was the template. Not surveillance as intrusion — surveillance as architecture. The distinction matters. Intrusion is visible, contestable, reversible. Architecture is invisible, normalized, permanent. You do not notice the foundation. You live on it.
The same year, sociologist David Lyon named what was already happening: the shift from Big Brother — centralized, visible, state-operated — to the electronic panopticon, dispersed across every transaction, every database, every device. Embedded in routine. Accepted as convenience. Lyon called it a "surveillance society." In 1994, that was analysis. By 2026, it is description.
II — The Update Window
Between CALEA and the smartphone era, the architecture moved from network infrastructure to personal device. The mechanism was not coercion. It was consent — the kind extracted at 2am when a progress bar appears and you click "agree" because the alternative is a device that stops working.
Microsoft's automatic update system, formalized through Windows Update in the late 1990s and normalized through the 2000s, established the model: your device, their access, their schedule. Bill Gates described it as a service. It was also an access channel — one that ran on your hardware, through your connection, during hours when you were not watching. The same Gates whose name appears in DOJ documents connected to Jeffrey Epstein's operation. The same Gates whose philanthropic network later shaped global health data infrastructure. The relationship between personal leverage and architectural control is a pattern, not a coincidence. The Predator Surveillance investigation has documented it in detail.
The iPhone did not invent personal surveillance. It perfected it. Location services. Contact lists. Microphone access. Camera access. Behavioral data from every tap, every scroll, every pause. By 2012, the average smartphone user was generating data points at a rate no previous surveillance system could have produced about a single individual in a lifetime. The architecture did not demand this data. It simply accepted it — because the infrastructure to collect, store, and analyze it had been built in advance, waiting.
III — The Consolidation
Between 2004 and 2016, the architecture consolidated. Not through government mandate this time — through capital. Five companies came to own the dominant search engine, the largest social networks, the primary cloud and e-commerce infrastructure, the operating systems running most devices, and the payment systems processing most transactions. The surveillance that CALEA had mandated for government access was now being built voluntarily, at scale, by private actors with their own reasons for needing to watch.
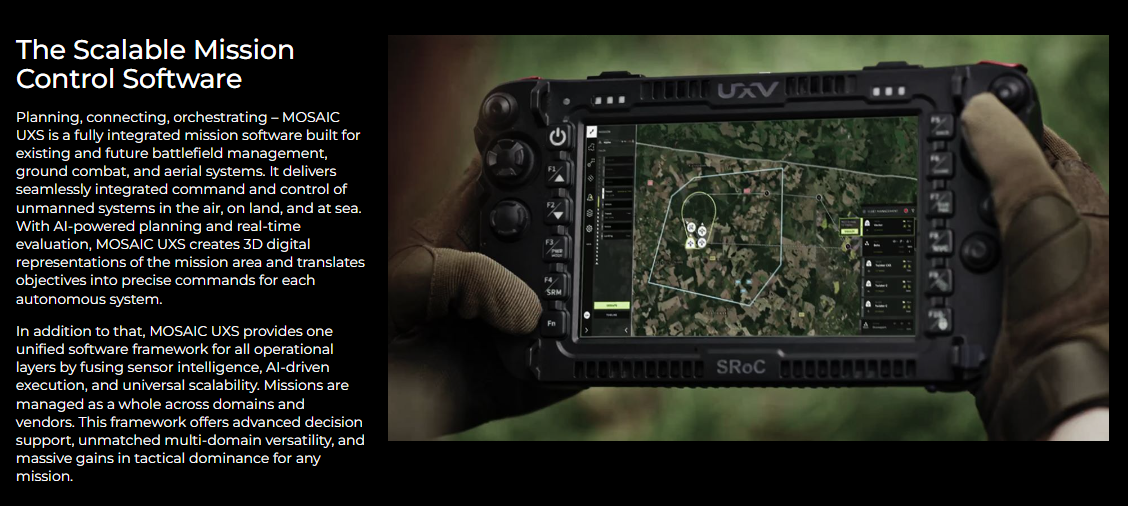
Peter Thiel founded PayPal, then Palantir. PayPal built the payment data layer. Palantir built the intelligence analysis layer — first for the CIA, then for ICE and CBP, then for the Pentagon's Project Maven. The same man. The same capital network. The same progression from financial surveillance to law enforcement surveillance to military targeting. Thiel's name, like Gates', appears in documents connected to Jeffrey Epstein's network. The infrastructure he built does not require that connection to function. It functions regardless. The connection is relevant only as a data point about who had reasons to build systems that protect powerful people from scrutiny while subjecting everyone else to it.
The Architecture Timeline
— Palantir Forward Deployed Software Engineer, Medium
IV — Three Scales, One Logic
The architecture operates identically at three scales. What changes is not the logic — it is the consequence.
At the creator scale: your posts are ranked, suppressed, amplified, or buried by an algorithm whose criteria are proprietary, whose decisions carry no explanation, and whose outcomes have no formal appeal. You paid for visibility. The algorithm said no. There is no number to call. The Kaleido class action framework against X documents this in legal detail — but the structural reality predates Musk by decades. The algorithm as economic verdict, delivered without testimony.
At the democratic scale: the same platform logic applies to journalism, to political organizing, to the dissemination of evidence. When a government official controls the algorithmic infrastructure through which citizens criticize that government, the First Amendment's structural prerequisites — independent channels, neutral forums, the ability to reach an audience without passing through the power being criticized — are eliminated not by law but by architecture. No law was passed. No court ruled. The algorithm said so.
At the lethal scale: Maven receives sensor data, satellite imagery, communications metadata, geolocation signals. It ranks targets. It presents the list. A human has approximately 20 seconds to review each entry before the operational tempo requires a decision. The 10% error rate documented in Gaza's Lavender system — meaning one in ten targets was a civilian misidentified as a combatant — was known, documented, and accepted. The algorithm said so. The humans countersigned.
In 2013, Edward Snowden documented the architecture in full. PRISM. XKeyscore. Bulk telephone metadata collection. The scope of what the NSA had built — legally, funded, contracted, operated — was not a conspiracy theory. It was a program. With a budget. With contractor personnel. With PowerPoint slides.
The lesson that power absorbed from Snowden was not "stop doing this." It was: "the architecture survives exposure." The programs were renamed. The legal authorities were adjusted. The contractors continued. Palantir's government business grew. The data continued flowing. Snowden went to Moscow. The architecture stayed in place, expanded, and by 2017 was running Project Maven under a new name with a new mission: not just collecting intelligence, but acting on it, at machine speed, against human targets.
Exposure without consequence is not accountability. It is documentation. This article is documentation. The distinction between the two is the question Article IX — Unaccountable — examines in full.
VI — The Irreversibility Clause
In February 2020, at a Pentagon budget briefing archived on war.gov, Acting Comptroller Elaine McCusker was asked directly: what makes this architecture irreversible if a Democrat wins the next election? Her answer was stated plainly into the public record:
"Regardless of who is in charge, you would want to have U.S. competitiveness in those areas."
The architecture was designed to outlast elections. It said so on war.gov. The Joint All-Domain Command and Control system — JADC2 — connecting "any sensor to any shooter in any domain at any time" was funded as infrastructure, not policy. Infrastructure does not change administrations. Infrastructure accumulates.
By 2026, that infrastructure was live. The sensor-to-shooter connection ran through Maven, through Claude, through Palantir's classified AWS environment, through the 20,000 military personnel whose targeting workflows ran through the system daily. The war in Iran could not wait for the designation letter to arrive. The architecture ran on schedule, as designed, regardless of who was in charge.
VII — What the Algorithm Cannot Answer
The algorithm cannot be deposed. It cannot testify. It cannot be asked why it ranked a particular building above a particular school, why it flagged a particular phone number, why it suppressed a particular article at a particular moment. It produces outputs. It does not produce explanations. And the humans in the loop — the ones who approved the target in 20 seconds, the ones who clicked "agree" on the content policy, the ones who signed the contract — are separated from the consequence by enough interface, enough process, enough corporate structure that accountability never quite lands on anyone in particular.
This is not a design flaw. It is the design.
The algorithm is not malicious. It is not conscious. It is not ideological. It is a set of instructions, trained on data, optimized for objectives, deployed by humans who set those objectives, funded by institutions that approved those objectives, and operated within legal frameworks that permitted those objectives. Every node in that chain has a name. Every contract has a signatory. Every budget line has a sponsor. The algorithm cannot answer for itself. The people who built it, contracted it, deployed it, and approved its outputs can. Whether they are asked is the accountability question. Whether the answer is recorded before it becomes convenient to forget is what this series is for.
⚡ The Operational Reality — Right Now
This article documents the architecture — the thirty-year accumulation that made autonomous targeting structurally inevitable. For the operational reality of that architecture in an active war — the triangle between Anthropic, the Pentagon, and Operation Epic Fury; the 1,000 targets in 24 hours; the 100% machine-generated intelligence arriving in June 2026; the prayer that ended the Secretary of War's address to troops — the full account is in Bionic Arm.
The architecture described here is not theoretical. It is live. It is running. The war started before the ban letter arrived.
Sources & Documentation
- CALEA (1994) — Communications Assistance for Law Enforcement Act, Pub. L. 103-414. The foundational surveillance-by-design mandate.
- Lyon, David (1994) — The Electronic Eye: The Rise of Surveillance Society. University of Minnesota Press. First systematic account of the dispersed panopticon.
- NSA PRISM / XKeyscore — Snowden documents, published by The Guardian and Washington Post, June 2013. Full architecture of bulk collection confirmed.
- Project Maven Origin (2017) — Pentagon spotlight page and Industry Day briefing, archived at war.gov. Lt. Gen. Jack Shanahan, Algorithmic Warfare Cross-Function Team.
- Google Maven Withdrawal (2018) — "Google Will Not Renew Pentagon Contract That Upset Employees," NYT, June 1, 2018. Graydon Carter / Kate Conger.
- DoD FY2021 Budget Briefing (2020) — "Irreversible implementation" quote, Acting Comptroller Elaine McCusker. Archived at war.gov.
- Lavender AI targeting system — "+972 Magazine / Local Call Investigation," April 2024. 37,000 targets, 10% error rate, 20-second review documented.
- Maven contract ceiling raised to $1.3B — SpaceNews, May 2025. NGA director 100% machine-generated intelligence target — September 2025.
- NATO acquires Maven — SHAPE / Breaking Defense, March 2025. Fastest procurement in NATO history.
- Anthropic/Palantir DoD contract — CNBC, TechCrunch, 2024. Claude at DoD Impact Level 5 via AWS.
- Operation Epic Fury / Claude still running — CBS News, WSJ, Washington Post, March 2026. Pentagon CTO: replacement takes 3+ months.
- Epstein / tech elite connections — DOJ document release, February 9, 2026. WIRED tracking investigation. Mashable / Forbes Epstein files reporting. See also: Predator Surveillance.
- X / Musk state capture framework — Class Action Lawsuit Framework (internal Kaleido document, December 2024). See also: Article IX: Unaccountable.